Learning software engineering opens the door to many job opportunities, but how do you know which one to pursue?
This article explores 7 software engineering disciplines, the skills involved, and the expected salary. We also look at an example of what your career path as a software engineer might look like—but remember, the journey will be different for everyone!
Types of software engineering jobs
Within software engineering are a whole array of disciplines to choose from. Finding programming jobs (and similar) is less daunting when you know what your options are and which discipline might suit you best.
1. Front-End engineer
Front-end engineers are responsible for how the front end of a site or application looks and how users can interact with it. They are responsible for planning, building, and implementing the user interface.
Front-end engineers must learn HTML, CSS, and JavaScript at a minimum. If you have an eye for design and an aptitude for improving user experience, you may be drawn to a career as a front-end engineer.
According to Indeed, the average salary for a front-end engineer in the UK is around £53,884.
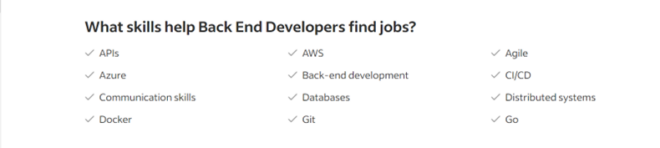
2. Back-End engineer
If the “front end” is the side that users see and interact with, then a back-end engineer is working behind the scenes on the particulars that make the application work. The “back end” includes server and server-side technologies like database design, data integration, and APIs.
Back-end engineers use a mix of programming languages, such as Java, Golang, Elixir, Python, and C++. If you’re interested in a career as a back-end engineer, it is also worth strengthening soft skills like problem-solving and collaboration.
According to Indeed, the average salary for a back-end engineer in the UK is around £60,801.
3. Full stack engineer
Combine the skills and responsibilities of front-end and back-end software engineers, and what do you get? A full stack engineer.
A full-stack engineer is a high-level software engineer who is expected to work across the entire system. They are responsible for designing, testing, and implementing various software applications, taking responsibility for APIs and databases as well as UX features and user interfaces.
You’ll notice that job titles like front-end, back-end, and full-stack engineer are quite general: you could be working on anything. For example, do you know the role of artificial intelligence in transportation? As technology continually develops, the possibilities for making a difference via coding skills are endless.
According to Indeed, the average salary for a full-stack engineer in the UK is around £55,780, although the high end is around £67,026.
4. Mobile app developer
Mobile developers build applications for tablets, smartphones, and other mobile devices. These applications will typically be on either iOS or Android operating systems, and engineers sometimes sub-specialise in one of the two.
Mobile app developers are similar to full-stack developers, since both need to cover the front and back ends of an app. They therefore need to be competent with user interfaces and back-end operations and should be proficient in languages like Java and Swift. Creativity and vision are a must to develop unique apps.
According to Indeed, the average salary for a mobile developer in the UK is around £40,627.
5. Graphic engineer
Graphic engineers usually focus either on video games or computer graphics. They tend to work with 2D/3D graphics, physics, and game mechanics.
Game development is perhaps one of the most exciting disciplines within graphics, and within software engineering overall. It is an opportunity to design characters and levels, write a story, and test a game that people can access and buy from games consoles, computers, smart phones, and more.
Specific requirements will differ depending on the project, but most game developers learn C++. This is a role for an individual with a flair for creativity, a passion for storytelling, and a desire to push boundaries in what video games can be.
It is more difficult to predict salary in more creative roles, but Glassdoor places the salary range between 20k and 40k in the UK.
6. DevOps engineer
DevOps engineers tend to be responsible for feature-facing work rather than client-facing work. Their job concerns infrastructure, automation, release cycles, and sometimes application health.
DevOps is short for developmental operations: the combination of practices, tools, and cultural philosophies that help an organization deliver applications and services at high velocity. In practice, that may look like managing the programs that allow an organization to deploy their software to big stacks of clusters.
To succeed as a DevOps engineer, you need to understand the fundamentals of the software development lifecycle (SDLC), including versioning strategies, source control management systems, and CI/CD pipelines.
Additionally, DevOPs engineers may be involved in managing programs like call center scheduling software, playing a key role in automating resource allocation and workflow for the organization.
According to Indeed, the average salary for a DevOps engineer in the UK is around £62,756.
7. Security engineer
Security engineers keep a company’s data and systems safe, taking responsibility for preventing hackers and cyber attacks while protecting against or removing viruses like ReceiverHelper Mac malware.

Tasks include:
- Planning network and hardware updates
- Implementing and monitoring an application’s security
- Testing for exploits
- Collaborating with other departments to safeguard sensitive data (e.g. in an IVR contact center, communications teams and security engineers would work to keep customer data secure).
- Responding to security incidents when they occur
To do this role well, security engineers should be skilled in a variety of coding languages plus penetration and vulnerability testing.
According to Indeed, the average salary for a security engineer in the UK is around £37,574.
What does a typical software engineer career path look like?
Whether you learn on the job, get a certification, or earn a Bachelor’s degree at a renowned institute like Torrens University Australia, there are numerous directions your career can take.
Let’s dive into an example software engineer career path:
Junior engineer
Most junior engineers are fresh out of university or college, and have little to no experience in professional software development.
In this role, they’ll gain experience working with a development team, learning new skills, how to contribute to projects, and how to work to project deadlines. You can expect a steep learning curve at this point in your career.
While you’re still getting a grasp of the fundamentals, it’s best to be open and receptive to feedback from senior developers.
Senior engineer
A senior engineer—typically someone with 5+ years experience—is generally regarded as the expert on the team. They have seen a plethora of different projects and technologies, and have mastered the software lifecycle.
Responsibilities include:
- Training new engineers
- Delivering code
- Working with data structures and algorithms
- Helping with larger initiatives
- Evaluating and executing long-term project goals
- Finding ways to improve output
- Ensuring product quality in the long term
At this stage, your career path starts to branch. You may choose a career in management, or you might decide to delve deeper into the technical realm.
Tech lead
This role varies between organizations, but is generally given to a candidate with 5+ years experience.
A tech lead works more closely with scoping project roadmaps for their teams and helping manage expectations with stakeholders. They’re responsible for making sure the team they are leading can work fluidly, removing any obstacles to productivity and success.
They may also take responsibility for domain management and testing—for example, if the company operates in multiple territories and has a Qa domain.
In some organizations this is purely technical/project work alongside leading a team, while in others being a tech lead is considered management experience.

Management
In a management role (again, 5+ years experience needed) much less time is spent on technical work. Instead, you’d be focusing on developing your team members in their careers, building a team to help meet the goals of the company, and managing stakeholders on projects.
Let’s look at some specific managerial positions:
Engineering manager (6+ years)
An engineering manager’s job is to manage a team of engineers day-today, building roadmaps and strategies for projects. They focus on building, coaching, and managing a team of high-performing engineers, and ensuring they deliver on expectations.
VP of engineering (10+ years)
This is a senior-level management position. The VP of engineering must lead and grow several teams, oversee project preparation and approval, organize budgets, oversee hiring, creatively problem-solve, and communicate strategies to other leadership. An upper manager may invest in a human resource information system (HRIS) to streamline HR tasks and manage employee data.
CTO (15+ years)
Chief Technology Officers (CTOs) are in charge of every technical aspect of a company, including engineering and other departments. They must be business-minded, with excellent communication and leadership skills.
Effective leadership development is crucial for CTOs to navigate the complexities of their role, inspire innovation, foster collaboration across teams, and drive strategic initiatives that align with the company’s goals and objectives.
Responsibilities include collaborating with the executive team to identify technical initiatives, developing and leading strategy for these initiatives, researching new technology systems, and reporting on KPIs and budgets.
Tips to get started on a software engineer career path
Practise your coding skills regularly
This should be a given if you’re serious about a career in software engineering. Coding skills are foundational to pretty much any discipline. Practicing on your own hones problem-solving and analytical skills, as well as building proficiency in essential coding languages.
Pursue software engineering courses or a bachelor’s degree in computer science
Before looking for entry-level positions, most software developers undertake a relevant university course, graduate training scheme, college course, or apprenticeship. This will usually be in computer science, information technology, or software development—although maths also has transferable skills.
Network
As in any career, it is important to network and make connections in the industry. If you’re not networking, then you’re likely missing out on roles and opportunities that you won’t find online. Additionally, networking provides a sense of community and keeps you up to date in the scene.
If you look online for communities and networking events, you’ll find plenty of options. Especially for women in tech, finding like-minded individuals can be everything.
Final thoughts
Whatever your skills and interests, there’s a software development role out there for you. Starting in an entry-level position as a junior software developer, you’ll find many opportunities throughout your career to specialisespecialize and grow. The key is to stay curious, keep learning, and make all the connections you can as you move along your chosen career path.

Jessica True is the Senior Director for Marketing Strategy and Operations at Dialpad, a modern business communications platform that takes every kind of conversation to the next level—turning conversations into opportunities. Jessica is an expert in collaborating with multifunctional teams to execute and optimize marketing efforts, for both company and client campaigns. She has written for other domains such as Agility PR Solutions and Developer Nation. Here is her LinkedIn.














