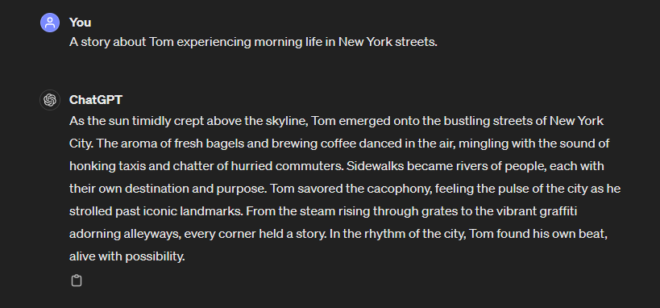
The way we build software is changing fast. Developers once spent days or even weeks writing boilerplate code, migrating between frameworks, or debugging repetitive logic. Today, AI coding tools are stepping in to handle many of these time-consuming tasks.
According to Jellyfish’s 2025 State of Engineering Management report, AI coding tool usage surged from just 14% of pull requests (PRs) in June 2024 to 51% by May 2025. Teams using AI saw average PR cycle times improve by 16% compared to those without AI, translating to 13.7 hours saved per PR. Code quality also remained consistent, with no meaningful increase in bugs.
The increase in AI usage can be attributed to the huge leap in AI capability. These tools have gone from basic syntax suggestions to full-on code generation. At first, tools like Tabnine and Kite offered intelligent code completion. Then GitHub Copilot introduced prompt-driven coding. Now, we’re seeing a new wave of AI platforms that don’t just suggest code, but build components, refactor architecture, and even migrate entire codebases.
This evolution means developers no longer need to start from scratch or wade through mountains of documentation. Instead, they can describe the component or feature they want and let the AI do the heavy lifting.
How AI Tools Build Software Components
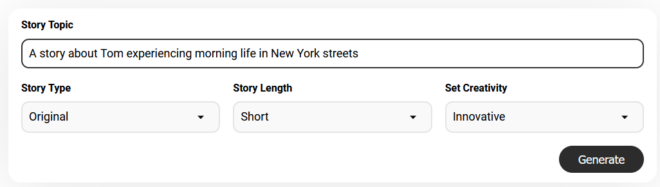
AI tools build software components by learning from billions of lines of public and proprietary code. With enough training data and fine-tuning, they can generate entire frontend components (buttons, forms, etc.), set up APIs and backend logic, automate testing and much more.
Want to build a login form with two-factor authentication? Describe it in natural language, and a modern AI coding assistant can scaffold the frontend component, set up backend API routes, and even suggest appropriate database models. Some platforms integrate directly with dev environments to allow for faster testing and debugging.
A prime example can be taken from component migration, a task that traditionally consumes significant dev hours. AutonomyAI’s CEO, Adir Ben-Yehuda, shared a case study during an interview with Eqvista, in which he describes the successful deployment of his company’s autonomous front-end coding platform to Deeto, an AI-powered customer marketing platform:
“One of our clients needed to migrate a substantial application from Angular to React—a daunting task that was estimated to take two months… We completed the migration in just five days. Not only was the turnaround remarkable, but the quality met production standards with minimal human revision. The client was thrilled, and it’s become one of our flagship proof points.”
Deeto helps businesses accelerate growth through customer storytelling. By cutting down the migration timeline from two months to just five days, it was able to roll out key features faster and without losing product momentum.
This kind of turnaround is becoming more common as dev teams integrate AI deeper into their workflows.
Balancing Speed With Context
The main advantage AI tools provide is speed. According to the Jellyfish report, 62% of engineering teams experienced at least a 25% boost in speed, while 8% claimed their output has doubled thanks to AI-assisted coding. This frees up a significant amount of developer time that can be redirected towards more high-impact and strategic tasks.
Equally as important, this productivity boost has not come at the cost of code quality. The same report found no meaningful increase in bugs for teams using AI tools. That said, it’s still best practice to have skilled developers review AI-generated output, especially in critical systems or when dealing with sensitive data.
That’s because while AI can generate production-grade code, it may lack enough business context to be able to make more informed architectural decisions. This also depends on the AI tool in use. Tools that are integrated directly into the development environment and have access to the full codebase, documentation, and workflows are generally better at producing context-aware output.
Real-Life Success Stories
The impact of AI in software development isn’t just theoretical. Aside from AutonomyAI, there are many other examples of engineering teams benefiting from AI in their workflows.
Zoominfo, a leading Go-to-Market Intelligence platform, recently rolled out GitHub Copilot across its engineering organization of more than 400 developers. As a result, 20% of all new code comes directly from Copilot-generated content. At the same time, developer satisfaction has improved, with three-quarters of developers reporting that the tool has positively impacted their productivity.
The financial giant, Morgan Stanley, has also implemented an in-house AI solution in an effort to modernize its COBOL-based legacy systems. Since its January 2025 launch, the tool has processed over 9 million lines of code, saving an estimated 280,000 developer hours.
Final Word
AI in software development is not an investment for the future, but for now. It’s already here, and real companies are seeing real results from integrating AI into their engineering workflows. In the not so distant future, we are likely to see AI agents embedded in every stage of the SDLC.
If you’re not already exploring how AI can support your development process, you risk falling behind as the rest of the industry moves faster and delivers more with less.